Secure Water Treatment (SWaT) is a water treatment site for cybersecurity research. SWaT was launched in 2015 by the iTrust Centre for Research in Cyber Security of the Singapore University of Technology and Design, with financial support from the Singapore Ministry of Defense
At the SWaT testbed, iTrust employees and partners study possible vectors for attacks against industrial facilities, and develop field-proven recommendations for critical infrastructure protection.
Photo and video courtesy of iTrust Centre
SWaT is a scaled-down replica of a full-fledged water treatment plant. The testbed simulates a modern water treatment facility consisting of six processes:
- P1: Raw water intake
- P2: Chemical disinfection
- P3: Ultrafiltration
- P4: Dechlorination using ultraviolet lamps
- P5: Purification by reverse osmosis
- P6: Ultrafiltration membrane backwash and cleaning
SWaT encompasses water purification equipment, several levels of communication networks, numerous PLCs, SCADA system, operator workstations, and storage of historical enterprise data. More details about SWaT are available on the iTrust website at the following links:
ITrust provided Kaspersky with a complete set of SWaT operational data: all network traffic and the values of 25 sensors and 26 actuators over a few days. The dataset reflects several days of normal operation of the testbed, followed by several days of various cyber-physical attacks. More information about the datasets can be found here.
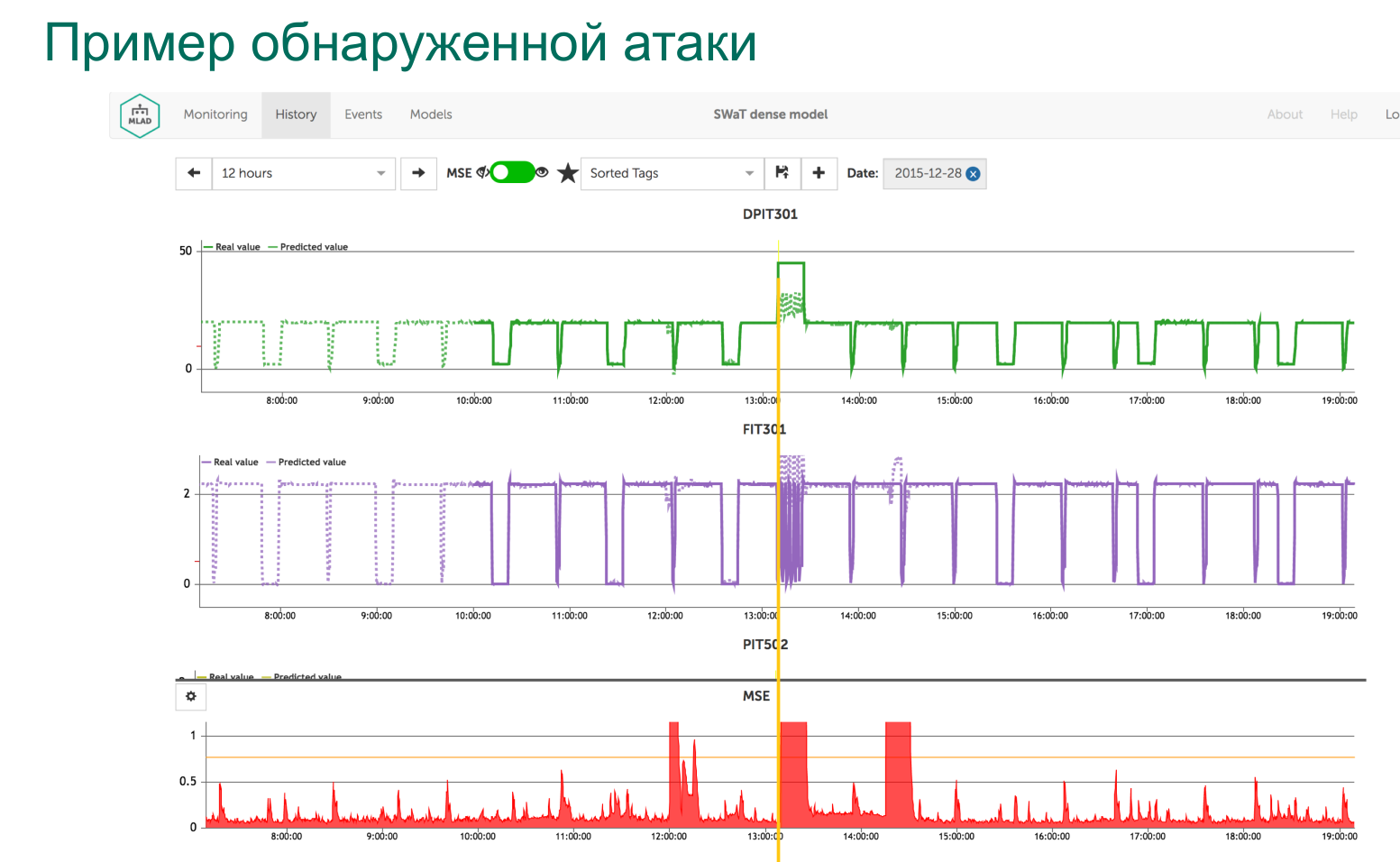
Based on the technical description of the testbed and the dataset provided, we created an ML model for SWaT. Using this ML model in Kaspersky MLAD, we:
- Successfully detected 23 of 34 attacks (9 of the undetected attacks had minimal impact).
- Correctly interpreted 22 of the 23 detected attacks.
- Detected 7 anomalies in the operation of SWaT not related to attacks and not previously known to the dataset compilers.